Google Workspace OAuth2
These are the steps I followed to implement OAuth2 authentication against Google Workspace.
Client Set Up
Setting up the client is a straightforward process. I created a new project in Google Workspace, and then added the necessary clients under that project.
Log in to Google Workspace as an administrative user and create a new project. I created an internal project as per our requirements. This also removes the necessity for having our application reviewed by Google.
Select the Branding menu on the left and provide the information related to your project.
Select the Data Access menu and add scopes you require. I added the following scopes:
userinfo.emailuserinfo.profileopenid
Select the Clients menu and create clients as necessary. I created three clients:
Local - for local development
Stage - for our staging environment.
Production - for our production environment.
I stored the client ID's, client secrets, redirect URIs, and other necessary information in config-db. Client secret values are stored encrypted
With these steps, I could move on to implementing the authentication flow.
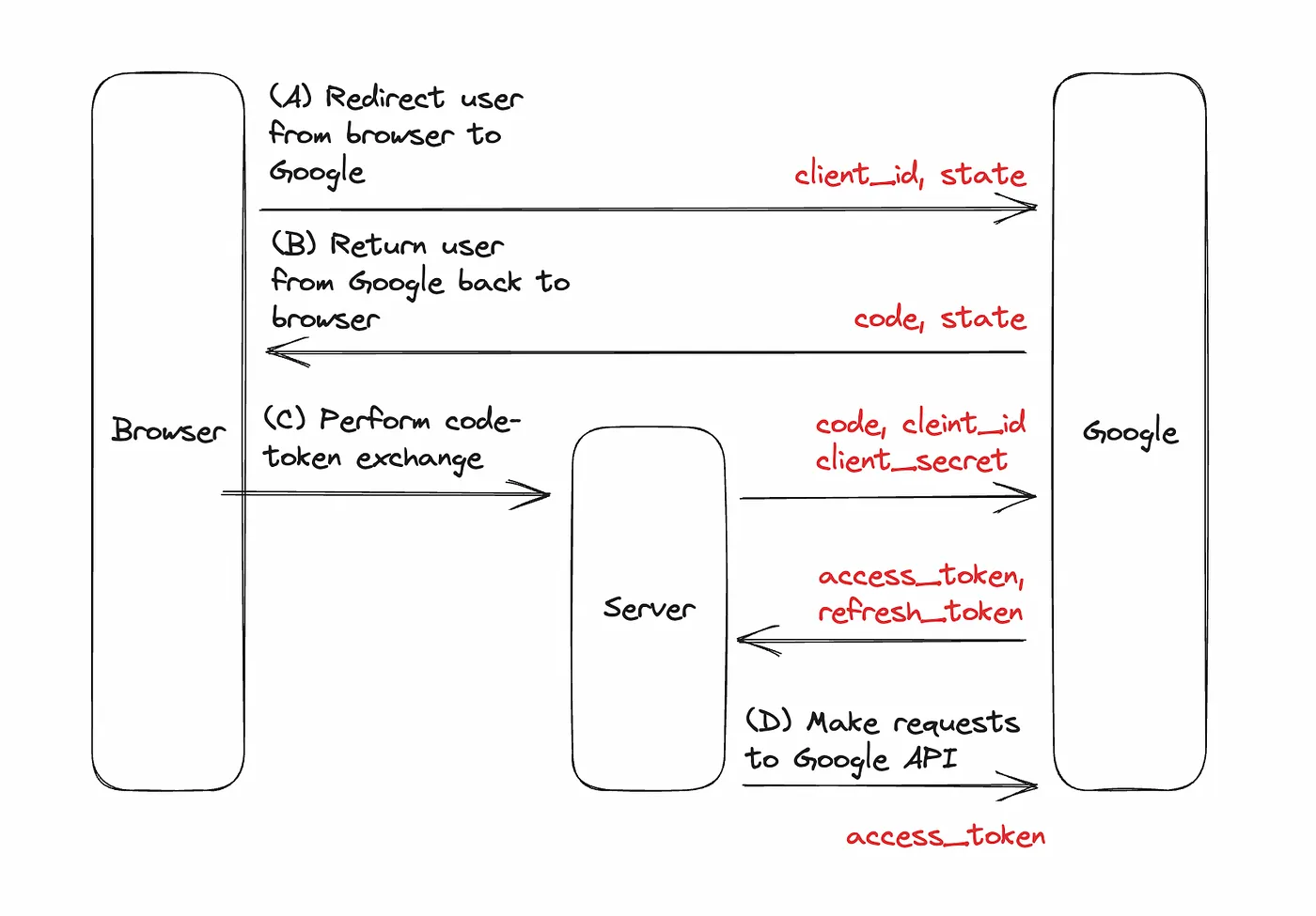
Authentication Flow
I followed the steps documented and had very little trouble getting the authentication flow to work. I was able to complete the entire setup and development in a few hours.
Wt Application
I extended our existing SSO application to support external authentication sources. We display a list of sources we support in a tab in the welcome screen on the application.
When the user clicks the Google Workspace button, we read the required information from the configuration database and redirect the user to the Google Workspace authentication page.
We create a new OIDC information record in the database and redirect the user to the Google Workspace authentication page. We use the encrypted value of the document ID as the state parameter. In the callback, we decrypt the state parameter and use it to retrieve the OIDC information record.
Callback Handler
The callback handler is implemented as a hidden endpoint in our API. The handler performs the following tasks:
Parse the query parameters returned by Google OAuth2 service.
Retrieve the OIDC information record from the database.
Exchange the authorisation code for an access token.
Create an internal user if not existing.
Generate a JWT token for the internal user.
Redirect the user to Wt application with updated OIDC information.
Parse the query parameters returned by Google OAuth2 service.
Retrieve the OIDC information record from the database.
A simple structure that represents the token information retrieved from the Google Workspace token exchange endpoint.
Exchange the authorisation code for an access token. Google also returns an id_token which is a JWT with the claims requested through the scope parameter. We use this information and avoid needing to make a request to the User Information endpoint.
Create an internal user if not existing.
Generate the JWT token for the internal user.
Redirect user to Wt application with updated OIDC information.
Receiver
A resource in the Wt application receives the redirect from the API callback handler. This is strictly not necessary, however, we create and manage the cookie for browser-based applications purely in the Wt application. This handler retrieves the JWT through the updated OIDC information and creates a cookie, which establishes a session for the user.